Security built for enterprise-grade reporting
Motley adheres to industry best practices in cloud security. This profile documents the controls protecting your data and systems — and welcomes your feedback to ensure our approach aligns with your policies and risk appetite.
GCP-native· TLS 1.2+ · AES-256· MFA-enforced · December 2025 version
.png)
Approve once. Delete anytime.
Every byte of client data is gated by explicit approval, encrypted in motion and at rest, and irreversibly erased when you ask.

Approve & ingest
Only client-approved, non-sensitive information enters the platform.

Process & retain
Data lives encrypted inside Google Cloud while it powers your reports.

Delete on request
One formal request and we erase everything we hold for you.
Ten controls, plainly written.

Data scope, lifecycle & LLM handling
Motley processes only client-approved, non-sensitive information, such as aggregated analytics, usage metrics, public content, and approved data from internal tools including databases, BI tools, and dashboards.
Ingestion filters are configured according to each client’s data-classification requirements to capture only approved fields and records.
Motley may store portions of client data relevant to slide decks and reports to support on-demand generation, and deletes this data upon formal client request.
Upon deletion, Motley permanently and irreversibly erases raw inputs, embeddings, derivative indices, and summaries from its systems.

Cloud infrastructure & encryption
Data processing occurs exclusively within Google Cloud Platform, GCP.
All data flows between client systems and Motley’s platform are protected via TLS 1.2+ encryption.
Data at rest is encrypted using AES-256, as provided by Google’s default encryption practices for GCP storage.
Security keys are managed by Google Cloud KMS.
Any backups are similarly securely encrypted.
.jpg)
Access control, authentication & secrets
Infrastructure and development access is strictly limited to engineering personnel and only as required to ensure functioning of the service.
Google Cloud IAM roles enforce least-privilege principles.
Multi-factor authentication, MFA, is mandated for all personnel accessing sensitive systems or data.
API keys and credentials are stored in encrypted form, with encryption keys managed in Google Cloud Secret Manager and regularly rotated.
Services retrieve secrets at runtime using a dedicated service account over TLS with a least-privilege “Secret Accessor” role.

Operational security, logging & monitoring
Motley adheres to secure coding practices, including mandatory code reviews for production code and minimal sensitive logging.
Employee workstations and laptops must have full-disk encryption enabled, up-to-date antivirus software with real-time protection, an active personal firewall, and automatic OS/application patching.
All application and infrastructure logs are maintained in Google Cloud Logging.
Logs are retained for operational troubleshooting for 30 days by default, with retention customizable based on client requirements.
Motley runs continuous security monitoring through Google Security Command Center for real-time threat detection and alerts.
.png)
Incident response
Motley aims to acknowledge critical incidents within 1 hour and resolve high-severity issues within 24 hours.
These targets are customizable based on client requirements.
The incident response process covers detection, containment, remediation, notification, and post-incident review.
Alerts are sent to the Motley team; temporary measures are taken to limit impact; the root cause is fixed; affected clients are informed; and lessons learned are identified.
Motley conducts incident-response drills and updates procedures at least twice a year, and immediately after any real incident.
.png)
Security testing, risk management & continuity
Motley uses automated dependency-vulnerability checks in CI/CD, secret scanning on every push, and reviewer checklists to block hard-coded credentials or unsafe patterns.
By Q1 2026, Motley plans to integrate lightweight SAST and fail builds on critical findings.
High-severity issues from any scanner are triaged within 48 hours and fixed according to Motley’s incident-response targets.
Motley conducts monthly lightweight security assessments of its codebase and cloud configuration, including third-party dependencies, cloud service configurations, IAM policies, and misconfiguration risks.
Identified risks are tracked in Motley’s issue tracker; high-severity findings are assigned an owner and remediation deadline.
All production databases and stores are backed up daily with GCP’s encrypted backups. Motley aims for an RTO of 4 hours and an RPO of 1 hour, revisiting these targets as infrastructure and client needs evolve.
The technologies behind every control
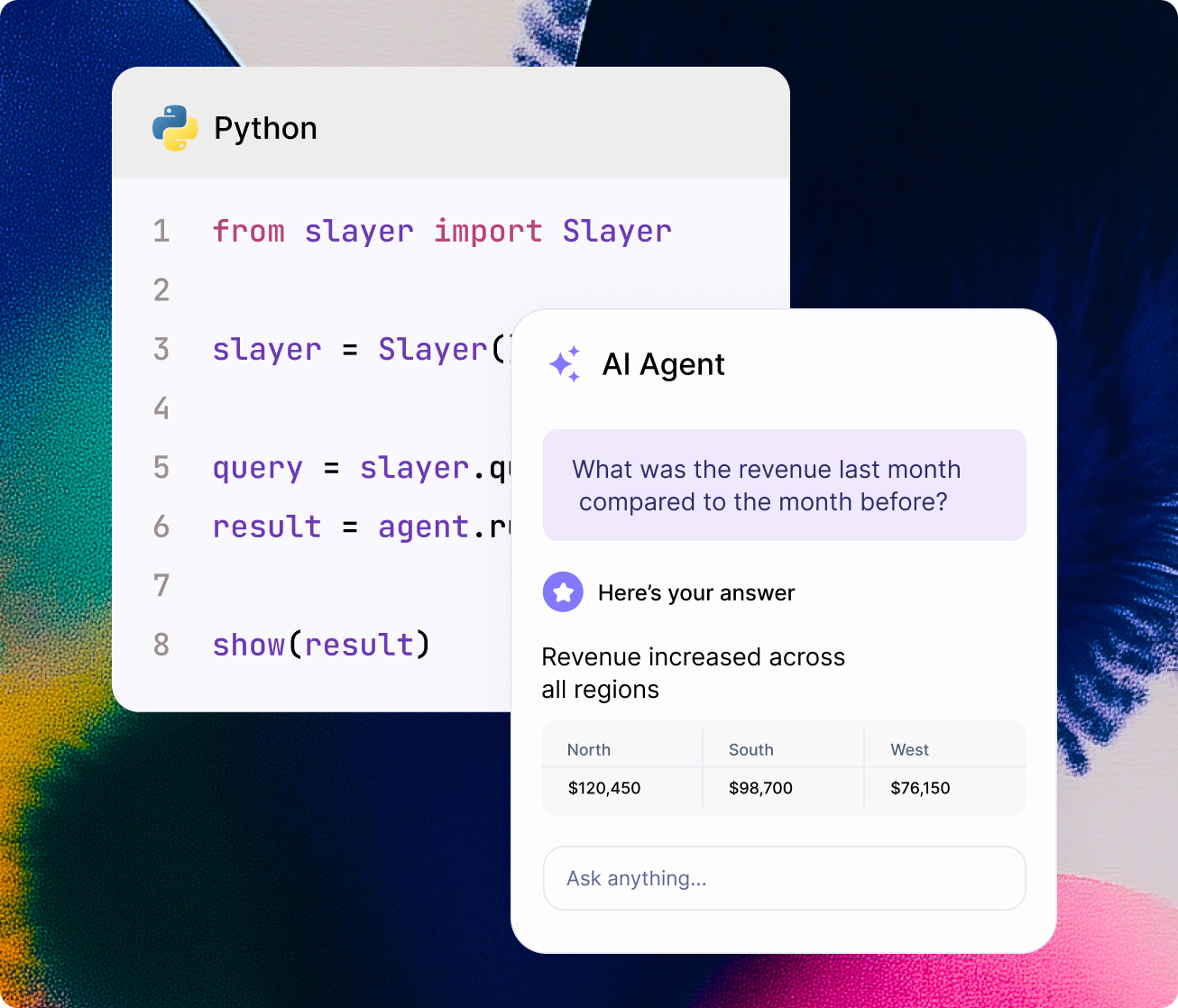
Designed for modern data workflows
SLayer works best in environments where queries are generated dynamically and reused across tools.